PyPI.org Phishing attack (original) (raw)
I just received this email (link deliberately broken):
As part of our ongoing account maintenance and security procedures, we’re asking users to verify their email addresses.
Please follow [this link](http s://pypj.org/account/login?user=ethan&token=xxx) to verify your email address.
This link will expire in 72 hours.
If you fail to confirm your email we may remove that email from your account to ensure your security.
Is pypj (that’s a J, not an I) one of ours?
MegaIng (Cornelius Krupp) July 26, 2025, 10:50pm 2
Definitely a fake website. If you check in the footer, some links like donate.pypj.org are broken because they aren’t quite spoofing everything and are instead trying to do a more simple pypi → pypj text replacement which doesn’t always work.
Probably worth reporting to google who are currently providing the certificate for this domain.
loic-simon (Loïc Simon) July 26, 2025, 10:54pm 3
stoneleaf (Ethan Furman) July 26, 2025, 11:31pm 4
Thanks, both! Site reported.
AA-Turner (Adam Turner) July 27, 2025, 1:00am 5
The site is also using Cloudflare name servers, and is registered with NameSilo LLC, so the abuse reporting for both firms can be used: https://abuse.cloudflare.com / abuse@namesilo.com. I’ve also sent an email to the PSF trademarks committee for obvious trademark infringement.
See https://rdap.namesilo.com/domain/pypj.org & ICANN Lookup.
A
EWDurbin (Ee Durbin) July 27, 2025, 11:01am 6
I have reports on the behalf of the PSF in at this time, and I’m aware that the trademark working group is also working from their angle. Thanks everyone.
malemburg (Marc-André Lemburg) July 27, 2025, 11:31am 7
Thanks for reporting this, @stoneleaf
I updated the title since this is a real attack. Perhaps we should send out a warning to users on one of the announcement and security channels.
This discussion is the top Google result when searching for “pypj.org”… I also received the same email verification request and was suspicious of the domain. I have a real pypi.org account associated with the same email the (fake) verification request was sent to.
I’m a nobody, so if I got this email there’s likely a lot more who also received the same phishing email. One of my projects was marked once as critical, so that could be the criteria they’re using for who to target.
Happy to provide email headers and any other info if requested.
webknjaz (🇺🇦 Sviatoslav Sydorenko (read: /sʋʲɑtɔˈslɑw/))
July 28, 2025, 9:16am 9
I got one too and just wanted to document that the email isn’t assigned to an actual PyPI account but is included in the core packaging meta and so it’s exposed publicly.
It’s a team@ address with forwarding to actual humans. And the scam “verification” URL just extracted the part before @ to inject into the GET param.
miketheman (Mike Fiedler)
July 28, 2025, 3:24pm 10
Hi gang,
Thanks for your diligence!
Some notices have gone up on social media, mailing lists, and PyPI blog:
Other efforts are underway to evaluate the impact and look at other prevention techniques.
EWDurbin (Ee Durbin)
July 28, 2025, 4:04pm 11
We have implemented a client side protection that should block the trivial proxy attacks like these, and are working with our CDN provider, Fastly, to determine if any of their security products would further protect us from these attacks.
EWDurbin (Ee Durbin)
July 28, 2025, 4:21pm 12
Cloudflare has also now flagged to the domain.
EWDurbin (Ee Durbin) July 28, 2025, 4:51pm 13
The domain registrar has also placed this domain on a hold.
miketheman (Mike Fiedler)
July 31, 2025, 5:10pm 14
The incident is over, and here’s a deeper dive.
webknjaz (🇺🇦 Sviatoslav Sydorenko (read: /sʋʲɑtɔˈslɑw/))
September 26, 2025, 10:47pm 15
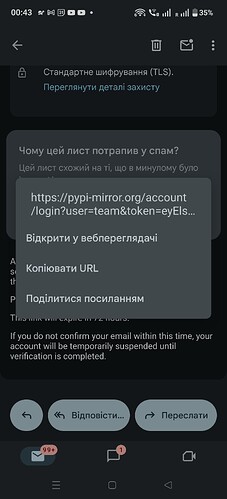
Looks like there’s a new phishing domain with similar attack mechanics — I’ve found this 3-days old thing in my spam folder:
sethmlarson (Seth Michael Larson) September 26, 2025, 11:06pm 16
Thanks for reporting, we responded additionally to the new domain: Phishing attacks with new domains likely to continue - The Python Package Index Blog
It’s likely this will continue with different domains, so we might start re-using blog posts with slight updates to avoid needing to constantly emit the same recommendations with only the domain name changed.