Publications Archive | Page 2 of 15 | PQShield (original) (raw)
0
Peer-Reviewed
Papers
0
Further NIST PQC
Submissions
0
NIST PQC Standards
Co-Authored
0
Patents in
Process
0
Mature Products
Developed
0
Best Paper
Awards

SPOTLIGHT PUBLICATION | 09/04/2026Breaking Silos: Resilience as a Cross-Functional MandateIn this episode of Shielded:, Jo speaks with Carolina Polito, a researcher at the Center for European Policy Studies and a PhD candidate in international relations. 

| 19/03/2026Mapping the Supply Chain: A Faster Path to Organizational ResilienceIn this episode of Shielded, Jo Lintzen speaks to Sarah McCarthy, Quantum Readiness Program Lead at Citi, who shares how Citi's quantum readiness program has evolved since 2022. They discuss supply chain readiness, and why the first step toward quantum safety does not require a dedicated team or advanced algorithms.
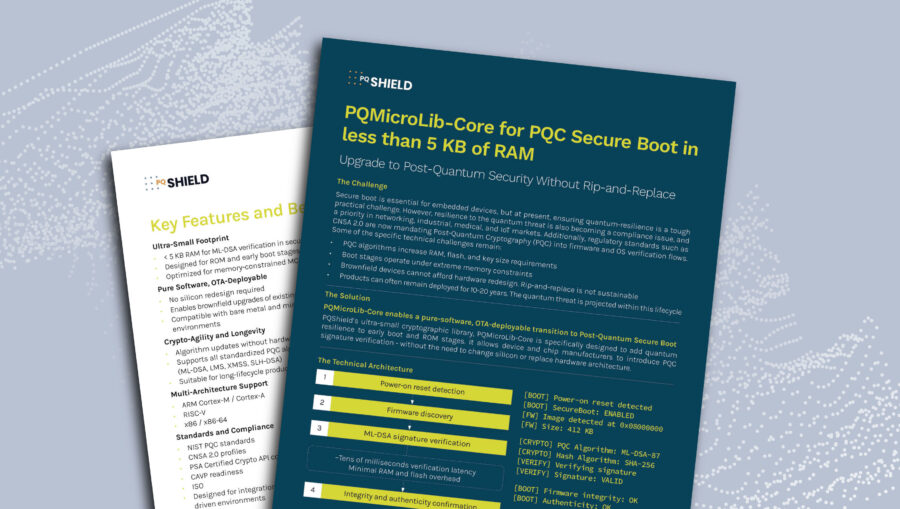
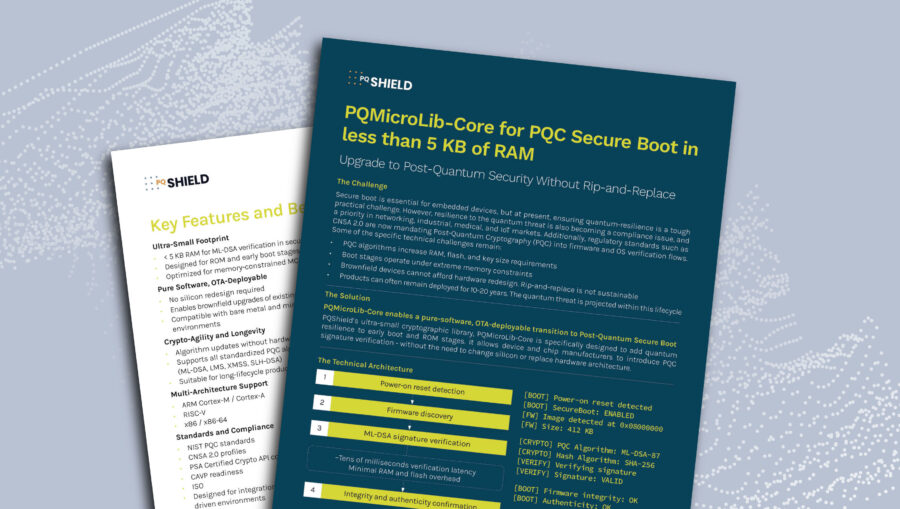
| 18/03/2026Solution Brief: PQMicroLib-Core for PQC Secure Boot in less than 5 KB of RAMThis Brief explains how PQShield PQMicroLib-Core enables a pure-software, OTA-deployable transition to Post-Quantum Secure Boot. PQShield’s ultra-small cryptographic library, PQMicroLib-Core is specifically designed to add quantum resilience to early boot and ROM stages. Read more.
Show All
Solution Briefs
Podcasts
Videos
Best Paper
Research Papers
Whitepapers
Filter by:
 | 26/01/2026A Lattice-Based IND-CCA Threshold KEM from the BCHK+ TransformIn this paper, we present a simpler, more efficient way to create a secure, quantum-resistant shared "vault" (a threshold KEM) without using overly complex or slow mathematical tools. It's achieved by combining established cryptographic frameworks with a new, proven mathematical assumption called Coset-Hint-MLWE. The result is a highly secure system that is easier to implement and more practical for real-world use than previous versions.
| 26/01/2026A Lattice-Based IND-CCA Threshold KEM from the BCHK+ TransformIn this paper, we present a simpler, more efficient way to create a secure, quantum-resistant shared "vault" (a threshold KEM) without using overly complex or slow mathematical tools. It's achieved by combining established cryptographic frameworks with a new, proven mathematical assumption called Coset-Hint-MLWE. The result is a highly secure system that is easier to implement and more practical for real-world use than previous versions.
 | 09/01/2026How to Compare Two-Party Secure Messaging Protocols: A Quest for A More Efficient and Secure Post-Quantum ProtocolRecent efforts to transition secure messaging to post-quantum standards, like Apple’s PQ3 and Signal’s updated Triple Ratchet, have introduced complex design trade-offs due to the high communication overhead of post-quantum cryptography. This paper introduces a pragmatic metric and experimental framework to compare these protocols, revealing that no "optimal" protocol exists when balancing security against real-world bandwidth constraints. Additionally, the authors propose a new optimization called "opportunistic sending" and a building block termed "sparse continuous key agreement" to improve protocol efficiency.
| 09/01/2026How to Compare Two-Party Secure Messaging Protocols: A Quest for A More Efficient and Secure Post-Quantum ProtocolRecent efforts to transition secure messaging to post-quantum standards, like Apple’s PQ3 and Signal’s updated Triple Ratchet, have introduced complex design trade-offs due to the high communication overhead of post-quantum cryptography. This paper introduces a pragmatic metric and experimental framework to compare these protocols, revealing that no "optimal" protocol exists when balancing security against real-world bandwidth constraints. Additionally, the authors propose a new optimization called "opportunistic sending" and a building block termed "sparse continuous key agreement" to improve protocol efficiency.
 | 08/01/2026The End of Static Cryptography: What Leaders Must Understand NowThis special episode of Shielded brings together experts from cryptography, security architecture, and risk to explain what comes next. The conversation clarifies that security can no longer rely on fixed algorithms or one-time upgrades.
| 08/01/2026The End of Static Cryptography: What Leaders Must Understand NowThis special episode of Shielded brings together experts from cryptography, security architecture, and risk to explain what comes next. The conversation clarifies that security can no longer rely on fixed algorithms or one-time upgrades.
 19/12/2025Subversion-resilient key-exchange in the post-quantum worldThis paper enhances subversion-resilient Authenticated Key Exchange (AKE) by using "Reverse Firewalls" to protect protocols against tampered implementations. Key contributions include Flexible Security Framework - a new definition that focuses on restoring specific security properties (authentication and key security) across various levels of compromise, Post-Quantum Readiness: the introduction of re-randomizable Key Encapsulation Mechanisms (KEMs), with implementations based on both Diffie-Hellman and Kyber, and Formal Verification - rigorous validation of the protocol using both traditional computational proofs and the CryptoVerif formal prover.
19/12/2025Subversion-resilient key-exchange in the post-quantum worldThis paper enhances subversion-resilient Authenticated Key Exchange (AKE) by using "Reverse Firewalls" to protect protocols against tampered implementations. Key contributions include Flexible Security Framework - a new definition that focuses on restoring specific security properties (authentication and key security) across various levels of compromise, Post-Quantum Readiness: the introduction of re-randomizable Key Encapsulation Mechanisms (KEMs), with implementations based on both Diffie-Hellman and Kyber, and Formal Verification - rigorous validation of the protocol using both traditional computational proofs and the CryptoVerif formal prover.
 | 19/12/2025Confidentiality vs Authentication: How Far the Web Has Actually MovedIn this episode of Shielded Jo Lintzen speaks with Sofia Celi, Senior Cryptography and Security Researcher at Brave, co-author of the MAYO signature scheme, and co-chair of an IETF working group driving global PQC standards.
| 19/12/2025Confidentiality vs Authentication: How Far the Web Has Actually MovedIn this episode of Shielded Jo Lintzen speaks with Sofia Celi, Senior Cryptography and Security Researcher at Brave, co-author of the MAYO signature scheme, and co-chair of an IETF working group driving global PQC standards.
 | 04/12/2025The Hidden Threat: Harvest-Now-Forge-Later and the Collapse of Digital TrustIn this episode of Shielded, Jo Lintzen speaks with Kevin Reifsteck, Director for Critical Infrastructure Protection at Microsoft, about how governments and global enterprises can turn quantum-safe readiness from policy into practice.
| 04/12/2025The Hidden Threat: Harvest-Now-Forge-Later and the Collapse of Digital TrustIn this episode of Shielded, Jo Lintzen speaks with Kevin Reifsteck, Director for Critical Infrastructure Protection at Microsoft, about how governments and global enterprises can turn quantum-safe readiness from policy into practice.
 | 24/11/2025Solution brief: PQShield’s PQCryptoLib-SDK and Nexus certificate management solutionThe document describes how PQShield's PQCryptoLib-SDK integrates with Nexus Certificate Manager (CM), Nexus's PKI platform, to create a post-quantum ready certificate management and VPN solution.
| 24/11/2025Solution brief: PQShield’s PQCryptoLib-SDK and Nexus certificate management solutionThe document describes how PQShield's PQCryptoLib-SDK integrates with Nexus Certificate Manager (CM), Nexus's PKI platform, to create a post-quantum ready certificate management and VPN solution.
 | 20/11/2025Inside Microsoft’s Quantum Safe Program: Turning Policy into PracticeIn this episode of Shielded, Jo Lintzen speaks with Kevin Reifsteck, Director for Critical Infrastructure Protection at Microsoft, about how governments and global enterprises can turn quantum-safe readiness from policy into practice.
| 20/11/2025Inside Microsoft’s Quantum Safe Program: Turning Policy into PracticeIn this episode of Shielded, Jo Lintzen speaks with Kevin Reifsteck, Director for Critical Infrastructure Protection at Microsoft, about how governments and global enterprises can turn quantum-safe readiness from policy into practice.
 | 17/11/2025Ben Packman joins Web Summit Panel, Lisbon, 13 November 2025Our CSO Ben Packman speaking at Web Summit, Lisbon November 12:05-12:25 on – "Quantum crossroads: Opportunity and risk in the next computing era."
| 17/11/2025Ben Packman joins Web Summit Panel, Lisbon, 13 November 2025Our CSO Ben Packman speaking at Web Summit, Lisbon November 12:05-12:25 on – "Quantum crossroads: Opportunity and risk in the next computing era."
 14/11/2025Practical Deniable Post-Quantum X3DH: A Lightweight Split-KEM for K-WaayHow can you prove a private conversation ever happened? In modern secure messaging, the goal is "deniability"—ensuring no one can cryptographically prove you sent a message. This vital privacy feature is core to protocols like Signal's X3DH, but achieving it in a fully post-quantum world has been a major roadblock. A promising path forward involves 'split-KEMs' (a method for establishing secret keys), but previous approaches were too inefficient to be adopted. Our latest research, Sparrow-KEM, solves this efficiency problem. It makes this approach a viable way to upgrade the Signal protocol, making it fully resistant to quantum attackers. The results represent a significant leap forward...
14/11/2025Practical Deniable Post-Quantum X3DH: A Lightweight Split-KEM for K-WaayHow can you prove a private conversation ever happened? In modern secure messaging, the goal is "deniability"—ensuring no one can cryptographically prove you sent a message. This vital privacy feature is core to protocols like Signal's X3DH, but achieving it in a fully post-quantum world has been a major roadblock. A promising path forward involves 'split-KEMs' (a method for establishing secret keys), but previous approaches were too inefficient to be adopted. Our latest research, Sparrow-KEM, solves this efficiency problem. It makes this approach a viable way to upgrade the Signal protocol, making it fully resistant to quantum attackers. The results represent a significant leap forward...
 | 06/11/2025No-Regrets Migration: Why PKI Should Be Your First MoveHardware defines trust. If its cryptography fails, no amount of software protection can recover it. In this episode of Shielded, Jo Lintzen speaks with Thalia Laing, Principal Cryptographer at HP.
| 06/11/2025No-Regrets Migration: Why PKI Should Be Your First MoveHardware defines trust. If its cryptography fails, no amount of software protection can recover it. In this episode of Shielded, Jo Lintzen speaks with Thalia Laing, Principal Cryptographer at HP.
 | 23/10/2025Global Standards, Regional Variants: Designing for PQC Across JurisdictionsIn this episode of Shielded, Jo Lintzen speaks with Dr. Richard Searle, Chief AI Officer at Fortanix, about how confidential computing and a software-first model accelerate the shift to post-quantum cryptography.
| 23/10/2025Global Standards, Regional Variants: Designing for PQC Across JurisdictionsIn this episode of Shielded, Jo Lintzen speaks with Dr. Richard Searle, Chief AI Officer at Fortanix, about how confidential computing and a software-first model accelerate the shift to post-quantum cryptography.


 | 26/01/2026A Lattice-Based IND-CCA Threshold KEM from the BCHK+ TransformIn this paper, we present a simpler, more efficient way to create a secure, quantum-resistant shared "vault" (a threshold KEM) without using overly complex or slow mathematical tools. It's achieved by combining established cryptographic frameworks with a new, proven mathematical assumption called Coset-Hint-MLWE. The result is a highly secure system that is easier to implement and more practical for real-world use than previous versions.
| 26/01/2026A Lattice-Based IND-CCA Threshold KEM from the BCHK+ TransformIn this paper, we present a simpler, more efficient way to create a secure, quantum-resistant shared "vault" (a threshold KEM) without using overly complex or slow mathematical tools. It's achieved by combining established cryptographic frameworks with a new, proven mathematical assumption called Coset-Hint-MLWE. The result is a highly secure system that is easier to implement and more practical for real-world use than previous versions.  | 09/01/2026How to Compare Two-Party Secure Messaging Protocols: A Quest for A More Efficient and Secure Post-Quantum ProtocolRecent efforts to transition secure messaging to post-quantum standards, like Apple’s PQ3 and Signal’s updated Triple Ratchet, have introduced complex design trade-offs due to the high communication overhead of post-quantum cryptography. This paper introduces a pragmatic metric and experimental framework to compare these protocols, revealing that no "optimal" protocol exists when balancing security against real-world bandwidth constraints. Additionally, the authors propose a new optimization called "opportunistic sending" and a building block termed "sparse continuous key agreement" to improve protocol efficiency.
| 09/01/2026How to Compare Two-Party Secure Messaging Protocols: A Quest for A More Efficient and Secure Post-Quantum ProtocolRecent efforts to transition secure messaging to post-quantum standards, like Apple’s PQ3 and Signal’s updated Triple Ratchet, have introduced complex design trade-offs due to the high communication overhead of post-quantum cryptography. This paper introduces a pragmatic metric and experimental framework to compare these protocols, revealing that no "optimal" protocol exists when balancing security against real-world bandwidth constraints. Additionally, the authors propose a new optimization called "opportunistic sending" and a building block termed "sparse continuous key agreement" to improve protocol efficiency.  | 08/01/2026The End of Static Cryptography: What Leaders Must Understand NowThis special episode of Shielded brings together experts from cryptography, security architecture, and risk to explain what comes next. The conversation clarifies that security can no longer rely on fixed algorithms or one-time upgrades.
| 08/01/2026The End of Static Cryptography: What Leaders Must Understand NowThis special episode of Shielded brings together experts from cryptography, security architecture, and risk to explain what comes next. The conversation clarifies that security can no longer rely on fixed algorithms or one-time upgrades.  19/12/2025Subversion-resilient key-exchange in the post-quantum worldThis paper enhances subversion-resilient Authenticated Key Exchange (AKE) by using "Reverse Firewalls" to protect protocols against tampered implementations. Key contributions include Flexible Security Framework - a new definition that focuses on restoring specific security properties (authentication and key security) across various levels of compromise, Post-Quantum Readiness: the introduction of re-randomizable Key Encapsulation Mechanisms (KEMs), with implementations based on both Diffie-Hellman and Kyber, and Formal Verification - rigorous validation of the protocol using both traditional computational proofs and the CryptoVerif formal prover.
19/12/2025Subversion-resilient key-exchange in the post-quantum worldThis paper enhances subversion-resilient Authenticated Key Exchange (AKE) by using "Reverse Firewalls" to protect protocols against tampered implementations. Key contributions include Flexible Security Framework - a new definition that focuses on restoring specific security properties (authentication and key security) across various levels of compromise, Post-Quantum Readiness: the introduction of re-randomizable Key Encapsulation Mechanisms (KEMs), with implementations based on both Diffie-Hellman and Kyber, and Formal Verification - rigorous validation of the protocol using both traditional computational proofs and the CryptoVerif formal prover.  | 19/12/2025Confidentiality vs Authentication: How Far the Web Has Actually MovedIn this episode of Shielded Jo Lintzen speaks with Sofia Celi, Senior Cryptography and Security Researcher at Brave, co-author of the MAYO signature scheme, and co-chair of an IETF working group driving global PQC standards.
| 19/12/2025Confidentiality vs Authentication: How Far the Web Has Actually MovedIn this episode of Shielded Jo Lintzen speaks with Sofia Celi, Senior Cryptography and Security Researcher at Brave, co-author of the MAYO signature scheme, and co-chair of an IETF working group driving global PQC standards.  | 04/12/2025The Hidden Threat: Harvest-Now-Forge-Later and the Collapse of Digital TrustIn this episode of Shielded, Jo Lintzen speaks with Kevin Reifsteck, Director for Critical Infrastructure Protection at Microsoft, about how governments and global enterprises can turn quantum-safe readiness from policy into practice.
| 04/12/2025The Hidden Threat: Harvest-Now-Forge-Later and the Collapse of Digital TrustIn this episode of Shielded, Jo Lintzen speaks with Kevin Reifsteck, Director for Critical Infrastructure Protection at Microsoft, about how governments and global enterprises can turn quantum-safe readiness from policy into practice. 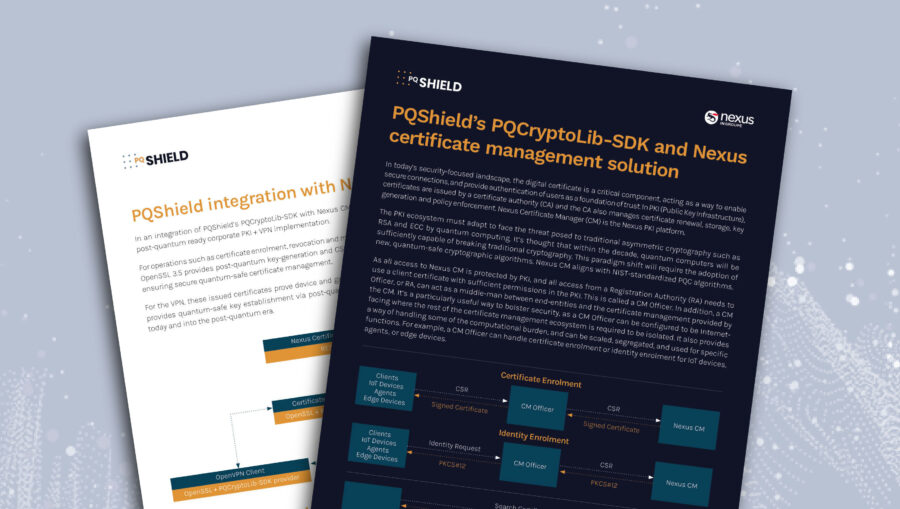 | 24/11/2025Solution brief: PQShield’s PQCryptoLib-SDK and Nexus certificate management solutionThe document describes how PQShield's PQCryptoLib-SDK integrates with Nexus Certificate Manager (CM), Nexus's PKI platform, to create a post-quantum ready certificate management and VPN solution.
| 24/11/2025Solution brief: PQShield’s PQCryptoLib-SDK and Nexus certificate management solutionThe document describes how PQShield's PQCryptoLib-SDK integrates with Nexus Certificate Manager (CM), Nexus's PKI platform, to create a post-quantum ready certificate management and VPN solution.  | 20/11/2025Inside Microsoft’s Quantum Safe Program: Turning Policy into PracticeIn this episode of Shielded, Jo Lintzen speaks with Kevin Reifsteck, Director for Critical Infrastructure Protection at Microsoft, about how governments and global enterprises can turn quantum-safe readiness from policy into practice.
| 20/11/2025Inside Microsoft’s Quantum Safe Program: Turning Policy into PracticeIn this episode of Shielded, Jo Lintzen speaks with Kevin Reifsteck, Director for Critical Infrastructure Protection at Microsoft, about how governments and global enterprises can turn quantum-safe readiness from policy into practice.  | 17/11/2025Ben Packman joins Web Summit Panel, Lisbon, 13 November 2025Our CSO Ben Packman speaking at Web Summit, Lisbon November 12:05-12:25 on – "Quantum crossroads: Opportunity and risk in the next computing era."
| 17/11/2025Ben Packman joins Web Summit Panel, Lisbon, 13 November 2025Our CSO Ben Packman speaking at Web Summit, Lisbon November 12:05-12:25 on – "Quantum crossroads: Opportunity and risk in the next computing era."  14/11/2025Practical Deniable Post-Quantum X3DH: A Lightweight Split-KEM for K-WaayHow can you prove a private conversation ever happened? In modern secure messaging, the goal is "deniability"—ensuring no one can cryptographically prove you sent a message. This vital privacy feature is core to protocols like Signal's X3DH, but achieving it in a fully post-quantum world has been a major roadblock. A promising path forward involves 'split-KEMs' (a method for establishing secret keys), but previous approaches were too inefficient to be adopted. Our latest research, Sparrow-KEM, solves this efficiency problem. It makes this approach a viable way to upgrade the Signal protocol, making it fully resistant to quantum attackers. The results represent a significant leap forward...
14/11/2025Practical Deniable Post-Quantum X3DH: A Lightweight Split-KEM for K-WaayHow can you prove a private conversation ever happened? In modern secure messaging, the goal is "deniability"—ensuring no one can cryptographically prove you sent a message. This vital privacy feature is core to protocols like Signal's X3DH, but achieving it in a fully post-quantum world has been a major roadblock. A promising path forward involves 'split-KEMs' (a method for establishing secret keys), but previous approaches were too inefficient to be adopted. Our latest research, Sparrow-KEM, solves this efficiency problem. It makes this approach a viable way to upgrade the Signal protocol, making it fully resistant to quantum attackers. The results represent a significant leap forward...  | 06/11/2025No-Regrets Migration: Why PKI Should Be Your First MoveHardware defines trust. If its cryptography fails, no amount of software protection can recover it. In this episode of Shielded, Jo Lintzen speaks with Thalia Laing, Principal Cryptographer at HP.
| 06/11/2025No-Regrets Migration: Why PKI Should Be Your First MoveHardware defines trust. If its cryptography fails, no amount of software protection can recover it. In this episode of Shielded, Jo Lintzen speaks with Thalia Laing, Principal Cryptographer at HP.  | 23/10/2025Global Standards, Regional Variants: Designing for PQC Across JurisdictionsIn this episode of Shielded, Jo Lintzen speaks with Dr. Richard Searle, Chief AI Officer at Fortanix, about how confidential computing and a software-first model accelerate the shift to post-quantum cryptography.
| 23/10/2025Global Standards, Regional Variants: Designing for PQC Across JurisdictionsIn this episode of Shielded, Jo Lintzen speaks with Dr. Richard Searle, Chief AI Officer at Fortanix, about how confidential computing and a software-first model accelerate the shift to post-quantum cryptography.