Tips for smoother, more secure cloud performance (original) (raw)
It's easy for an unanticipated glitch to create a significant disruption to a cloud environment. To get around these pitfalls, here are some key things to watch out for.
Browsing a website that operates mainly in the cloud environment means you're most likely taking for granted the 24/7 access and that personal data is secure. With that level of expectation, a site operator needs to make sure backend cloud services behave controllably.
That means ensuring two important factors: Services must run without interruption, and sound security practices must allow system access only at specific times and with limited privileges when necessary.
What are backend cloud services?
Backend cloud services are the operations and routines end users don't see. These are often referred to as east-west traffic in AWS conference talks. The backend services in the cloud empower the frontend services to power up user interfaces. Backend services could include collating, analyzing and sending requested data.
When those backend cloud services fail, whether due to unexpected spikes in demand or unforeseen results of configuration changes, it can damage a company's reputation. It's essential to secure the storage and distribution of access keys, to operate with the principle of least privilege and to safeguard inter-service communications.
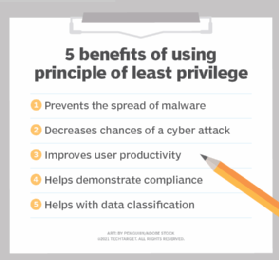
By restricting access to a cloud environment, an organization can lower its security risks.
Digital security terminology
Every industry has its own language. When it comes to digital security in the cloud, there are some key terms to know and understand:
- Service account. This account is used by an application or computer workload, such as a cloud-based app, rather than a person (user account).
- Access key messages. These are long-term credentials, which in AWS are used to sign programmatic requests to the AWS Command Line interface or AWS API Gateway.
- Service mesh. Service mesh is a dedicated infrastructure layer for facilitating service-to-service communications between services or microservices.
- Digital certificate. This file verifies a user's or service's identity and enables encrypted communications.
Managing access to backend services
Developers who build websites or backend services need to meet the needs of customers. To do this, they can avoid potential breaches and security issues by following and establishing these best practices:
- Keep the number of people with access to high-level data to a minimum. Follow the least privilege model to permit only the access that's absolutely necessary to the service account.
- Store security keys appropriately. Storing access keys or service credentials in code is unwise. Use an external key vault or secrets manager to encrypt sensitive data, including access keys. For added protection, explore using cloud-based key management systems and hardware security modules.
- Update, rotate or change service account credentials regularly. When API access keys expire before they are updated, that can result in an outage. Update access keys regularly and avoid credentials that never expire.
- Avoid using the same service accounts for multiple services. Be conscious of multiple users sharing accounts_._ Decommission service accounts when no longer needed. Track all the places where the service accounts are in use.
- Stay current with automated tools. These tools can help take the labor out of managing service accounts to keep backend cloud services secure. Features include automatic renewal of keys or certificates, the cataloging of service principals and profiling permissions, and managing of privileges assigned to service accounts.
Cloud platforms offer innovations
Most cloud platforms enable users to manage credentials and observe and secure services without changing access keys. Important strategies for securing services and minimizing outages include using an automated certificate management tool, auditing access to services, time-bound access for on-call engineers, and secure key storage.
On AWS, AWS Secrets Manager enables users to rotate, manage and retrieve database credentials, API keys and other secrets through their lifecycle. Temporary security credentials can be configured to expire after a few minutes or several hours.
Security enhancements offered by Google Cloud, Microsoft Azure and other cloud providers are continuously evolving. Observability suites, for example, are software packages that, once fully integrated, can track system behavior. They provide warnings about security or operational trouble. Microsoft Azure's managed identities feature entirely eliminates the need to manage credentials.
Some of the most prominent players in online services have experienced outages when no one noticed that certificates went out of date. Google Cloud's managed certificates feature automatically renews public certificates and updates apps when they run behind an external load balancer or in a managed Kubernetes engine.
A service mesh is a way to control how different parts of an application share data with one another. It is also a dedicated infrastructure layer built into an app. Istio is an open source service mesh, and the major cloud providers have all built their managed offerings. With service meshes, you can manage, observe and secure services without having to change service credentials. They can reduce or eliminate the need to manage service accounts at all.
Some of the most prominent players in online services have experienced outages when no one noticed that certificates went out of date.
The AWS App Mesh can manage and monitor microservices. This service offers users control of the communication and network traffic targeting those microservices. When the cloud handles mundane but critical administrative duties of backend services, IT departments and business units are free to take on more involved tasks.
Managing it all
Managing backend cloud services with the help of providers such as Google, AWS and Microsoft Azure can mean making frontend services appear to be seamless and reliable. But watch out for password rotations and security certificate expiration dates. Mutual authentication using private certificates can help. Cloud-managed PKI certificates can simplify administrative security tasks. For companies that can use microservices, service meshes can manage much of the infrastructure.
Watch for the security innovations and new automation features, as these can enable in-house teams to focus on work that leads to more productive programming and delivers business value.
Siddharth Bhai is a product management leader with 15-plus years of experience, including working at Google and Microsoft. He has extensive experience in identity management, security and cloud computing. Bhai is a frequent speaker at tech conferences. He can be reached at [email protected].
 By: Joe O’Halloran
By: Joe O’Halloran  What is a service mesh?
What is a service mesh?  By: Kinza Yasar
By: Kinza Yasar  Why and how to manage microservices without API gateways
Why and how to manage microservices without API gateways  By: Chris Tozzi
By: Chris Tozzi  Why a service mesh may not be for everyone
Why a service mesh may not be for everyone  By: Fleur Doidge
By: Fleur Doidge