Symmetric vs. asymmetric encryption: Understand key differences (original) (raw)
Explore the differences between symmetric vs. asymmetric encryption, including how they work and common algorithms, as well as their pros and cons.
Cryptography is the art of encrypting and decrypting data. Encryption is the process of encoding unencrypted data, or plaintext, into encrypted data, or ciphertext, to disguise the data and make it unreadable. Decryption is the method of decoding encrypted data into readable information.
Encryption algorithms, or ciphers, involve the use of a variable -- known as a key -- which makes the data unreadable. Only the person or entity with the proper decryption key is able to read the data.
Two widely used types of ciphers are symmetric and asymmetric. In a nutshell, symmetric encryption uses a single secret key, while asymmetric encryption involves a secret key pair.
Let's look at the two types of encryption, their pros and cons, use cases, and which to use when.
What is symmetric encryption and how does it work?
Symmetric encryption, also known as secret key encryption or single-key encryption, converts plaintext into ciphertext and back using a single secret key for both encryption and decryption.
Stream and block are the two types of symmetric algorithms. Stream ciphers encrypt data 1 bit at a time, while block ciphers encrypt data divided into set lengths, or blocks.
In a symmetric encryption example, sender Alice encrypts her message with an agreed-upon shared key and sends the encrypted message to Bob. Bob receives the encrypted message and uses the shared key to decrypt the message.
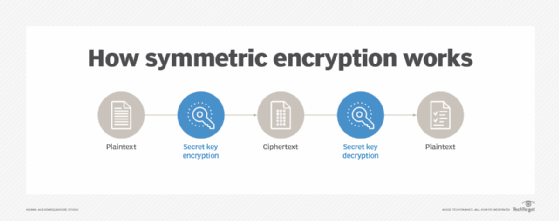
Symmetric encryption uses the same secret key to encrypt and decrypt messages.
Symmetric encryption algorithms
There are numerous types of symmetric encryption algorithms, including the following:
- Data Encryption Standard. Published in 1976, DES was the first modern symmetric encryption algorithm. The block cipher is no longer considered secure.
- Advanced Encryption Standard. AES is the most widely used algorithm in symmetric key cryptography. It was named successor to DES by NIST in 2001. AES comprises three block ciphers -- AES-129, AES-192 and AES-256 -- each of which is deemed sufficient to protect government-classified information up to the Secret level, with Top Secret information requiring either 192- or 256-bit key lengths.
- Triple DES (3DES). Also known as Triple Data Encryption Algorithm, or TDEA, 3DES is a block cipher that uses three 56-bit keys for a total of 168-bit strength. It is more secure than DES but not as strong as AES. NIST deprecated its use in new applications in 2017 and called for the full deprecation of 3DES through 2023, after which its use became disallowed.
- International Data Encryption Algorithm. IDEA has a typical block size of 64 bits. It is used in Pretty Good Privacy and its successor, OpenPGP.
- Blowfish**.** A 64-bit block cipher, Blowfish's small block size makes it vulnerable to attacks.
- Twofish**.** The successor of Blowfish, Twofish has a block size of 128 bits.
- Skipjack. This is a 64-bit block cipher developed by the National Security Agency. As of 2016, it is no longer certified to encrypt government data.
- Rivest Cipher 4. RC4 is a stream cipher. Attacks in the 2000s and 2010s revealed weaknesses in the RC4 algorithm, and the Internet Engineering Task Force prohibited its use in TLS in February 2015.
Uses of symmetric encryption include payment applications, validations and pseudo-random number generation or hashing.
Pros and cons of symmetric encryption
Pros of symmetric encryption include the following:
- Faster security. Symmetric encryption is faster to run because it only uses a single secret key and is based on less complicated mathematics.
- Ideal for big data sets. Symmetric encryption works well at encrypting large amounts of data.
- More secure. Symmetric encryption is more secure than asymmetric, especially once quantum computing becomes viable.
Cons of symmetric encryption include the following:
- No optimal method to securely share the key. Symmetric encryption requires sharing a secret key across an open network (internet), which increases the chance of compromise every time it's shared.
- Single point of failure. If the secret key used by both parties is compromised, both sides of the transaction are at risk and the data can be decrypted.
What is asymmetric encryption and how does it work?
Asymmetric encryption, also known as public key encryption, converts plaintext to ciphertext using two interdependent keys: one to encrypt the data, a public key, and another to decrypt the data encrypted with the public key, called a private key. Public keys can be used by anyone to encrypt the data. The private key, also known as a secret key, is known only to the entity decrypting the message.
In an asymmetric encryption example, sender Alice encrypts her message with a public key and sends the encrypted message to Bob. Bob receives the encrypted message and uses his private key to decrypt it.
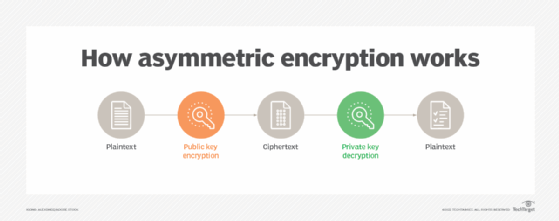
Asymmetric encryption uses a public and private key pair to encrypt and decrypt messages.
Using two different keys provides a number of different features, the most important probably being digital signatures. Among other things, digital signatures guarantee that a message was created by a particular entity. Digital signatures also authenticate remote systems or users.
It is important to note that current asymmetric algorithms are going to fall out of favor once cryptographically relevant quantum computers exist. Asymmetric algorithms rely on the difficulty of performing certain mathematical operations on classical computers, such as the factoring of large prime numbers. While it would take a classical computer thousands to billions of years to crack asymmetric encryption, a quantum computer will be able to in days or even hours.
By all estimates, quantum computing is still years away, but security experts warn about "harvest now, decrypt later" attacks in which malicious actors steal encrypted data now and decrypt it once the algorithms are crackable with quantum computers.
Asymmetric encryption algorithms
The most common asymmetric encryption algorithms include the following:
- Diffie-Hellman key exchange**.** The DH key exchange enables two parties to exchange cryptographic keys in a secure manner, regardless of whether the communication channel is public or private.
- Rivest-Shamir-Adleman. Based on DH, RSA is often used in e-commerce protocols and is believed to be secure given sufficiently long keys and the use of up-to-date implementations.
- Elliptic curve cryptography. Based on elliptic curve theory, ECC uses algebraic functions to generate security between key pairs.
Asymmetric cryptography is used in key exchange, email and web security, and cryptocurrencies, such as bitcoin.
Pros and cons of asymmetric encryption
Pros of asymmetric encryption include the following:
- Private keys are more secure. Private keys are never distributed or exchanged, keeping communications more secure.
- Public keys can be known by anyone without issue. The public key can be transmitted freely online or posted publicly without harming communications.
- Proof of origin and delivery. Digital signatures enable sender authentication because asymmetric encryption enables nonrepudiation.
Cons of asymmetric encryption include the following:
- Slower encryption speed. Asymmetric encryption is slower than symmetric.
- Locked out if private key is lost. If an entity loses its private key, messages can't be decrypted. If a private key is stolen, an attacker could use it to decrypt their messages.
- Public key ownership isn't authenticated. Users must verify that their public keys belong to them.
- Weak against quantum computing. Asymmetric encryption relies on solving mathematical equations that quantum computing excels at.
Asymmetric cryptography is subject to brute-force and man-in-the-middle attacks. Plus, if malicious hackers know either user's private key, they can use it to decrypt the data.
Importance of cryptographic hashing
A cryptographic hash function has a somewhat different role compared to other cryptographic algorithms. It is used to return a value based on a piece of data, such as a file or a message, for example. Any accidental or intentional change to the data changes this hash value.
A good hash algorithm should make it impossible to either create an initial input that produces a specific hash value or for the original input to be calculated from the hash value. Message-Digest 5, or MD5, and Secure Hash Algorithm 1 (SHA-1) were widely used hash algorithms that are now considered weak. They were deprecated in 2014 and were replaced by SHA-224, SHA-256, SHA-384 and SHA-512, collectively referred to as SHA-2. SHA-3 was released in 2015. It is composed of SHA-3-224, SHA-3-256, SHA-3-384 and SHA-3-512, as well as two extendable output functions, SHAKE128 and SHAKE256. SHA-3 was labeled a backup standard rather than a replacement for SHA-2.
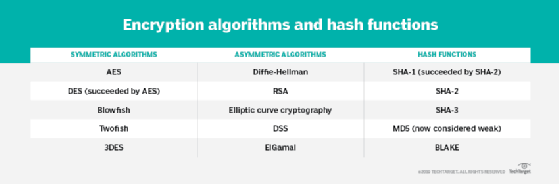
A variety of encryption algorithms and hash functions are available.
Symmetric vs. asymmetric: Which is better?
When choosing an encryption algorithm, it's important to consider the type of data being encrypted. High-risk or sensitive data, such as confidential customer information, needs stronger encryption than marketing plans, for example.
Performance is another key factor. Asymmetric encryption is generally slower than symmetric encryption due to the creation of two keys instead of one. The trade-off with symmetric encryption's use of the same key, however, is that there are multiple chances for that key to be exposed. Asymmetric encryption's distributed keys mean the private keys are never distributed and, therefore, are more secure.
As noted, symmetric and asymmetric encryption algorithms have different vulnerabilities. It is important to understand the application to match the most appropriate algorithm with the particular use case.
In many scenarios, such as SSL/TLS, both symmetric and asymmetric algorithms are used to boost security. Because asymmetric encryption is much slower than symmetric encryption, data is typically encrypted with a symmetric algorithm, and then the comparatively short symmetric key is encrypted using asymmetric encryption. This enables the key needed to decrypt the data to be securely sent to other parties along with the symmetrically encrypted data. In another example, Secure/Multipurpose Internet Mail Extensions, or S/MIME, uses an asymmetric algorithm for nonrepudiation and a symmetric algorithm for efficient privacy and data protection.
Key takeaways
The cryptography landscape is constantly changing, but both types of encryption have their use cases. Symmetric encryption remains useful for securing data at rest, such as for database protection and full-disk encryption. Asymmetric encryption is ideal for securing communications, such as with digital signatures and hashing symmetric keys.
Current asymmetric encryption algorithms won't secure data, however, once quantum computing becomes viable -- which is expected within the next five to 10 years.
Security experts recommend organizations begin to migrate from current asymmetric algorithms to quantum-safe algorithms vetted by NIST. Another option is to use a hybrid approach of current cryptographic standards and quantum-safe algorithms to keep data secure against both classical and quantum computers, enabling organizations to become crypto-agile in case an algorithm becomes crackable.
Michael Cobb, CISSP-ISSAP, is a retired security author with more than 20 years of experience in the IT industry.
Informa TechTarget editors revised this article in 2025 to improve the reader experience.
Dig Deeper on Data security and privacy
-
 What is HMAC (Hash-Based Message Authentication Code)?
What is HMAC (Hash-Based Message Authentication Code)?  By: Scott Robinson
By: Scott Robinson -
 Explore the impact of quantum computing on cryptography
Explore the impact of quantum computing on cryptography  By: Ryan Arel
By: Ryan Arel -
 What is a private key?
What is a private key?  By: Rahul Awati
By: Rahul Awati -
 What is a public key and how does it work?
What is a public key and how does it work?  By: Rahul Awati
By: Rahul Awati
Related Q&A from Michael Cobb
How to protect port 139 from SMB attacks
Keeping port 139 open is perfectly normal -- but only for good reason. Without the proper protections, it can present a major security risk.Continue Reading
Port scan attacks: What they are and how to prevent them
Port scans provide data on how networks operate. In the wrong hands, this info could be part of a larger malicious scheme. Learn how to detect and ...Continue Reading
Stateful vs. stateless firewalls: Understanding the differences
Stateful firewalls are the norm in most networks, but there are still times where a stateless firewall fits the bill. Learn how these firewalls work ...Continue Reading